Networking in information technology means the infrastructure between electronic devices, the wiring and the protocols for information exchange. Nowadays most devices are connected. This can occur locally, such as in a lift between control and drive, or via the internet, such as with a fitness bracelet.
Today most computers are permanently connected to the internet and communicate with servers or directly with other computers. The internet does not stop at the national border. We talk about global networking. The connected computers use IP addresses for addressing. These will be switched from IPv4 to IPv6 gradually. Here we explain, among other things, what an IPv6 is. Security plays an important role in the internet. We therefore also want to explain the possibilities of encryption via VPN. What VPN is and how it can be used can be found further down on this page.
IPv6
Via IP-addresses it is possible to unambiguously address a single device. Every device connected to an IP network receives an address that is unambiguous in the network. IP addresses are like postal addresses for computers and regulate the addressing of data. In the current, old form, the IPv4, IP addresses consist of four numbers from 0 to 255 (for example: 192.168.1.1). With the conversion to the protocol IPv6, which has been defined 10 years ago and is currently in its introductory phase, addresses of eight numbers in hexadecimal counting are introduced (for example: 2001:0db8:85a3:08d3:1319:8a2e:0370:7344). This is necessary because the old IPv4 protocol does not offer enough addresses anymore ('only' 4.3 billion) in order to assign an IP address to every device that is connected in the future. The conversion to IPv6 does not only offer more IP addresses, but also allows for the implementation of many services that rectify the disadvantages of the IPv4 network. More on the subject can be found at Wikipedia.
Gateways
Gateways are components meant to connect several networks that use different languages (protocols). They assume the role of mediation and translation of the messages between those networks. A WLAN router as used at home is a common example of a gateway. It mediates and translates protocols from the internet, such as they are transmitted via an ADSL transmission line, into the TCP/IP-protocol used in the home network or the USB protocols by which the connected printer is controlled. Another example would be an E-Mail-to-SMS gateway, which connects these two otherwise incompatible protocols with each other.
If a gateway translated the language of a network into the language of another it can occur that this information is lost, if the original information cannot be transported in the new network. In a lift the protocol CANopen-Lift is used on the internal field bus. This protocol provides information and control signals to the components in real time. A CANopen-Internet-Gateway establishes a connection to the internet an enables, for example, the remote diagnosis or configuration of the lift. To do so not all information has to be necessarily in real time, thus the loss of information is not relevant.
VPN
A VPN is a virtual private network. It enable the transport of data in a network that uses the infrastructure of another network. The data is tunneled through this other network. Since the data is transmitted with encryption a VPN is good procedure to access a distant network from a computer via the unsafe internet. With the help of VPN it is possible, for example, to log into a company network from the home office. The connection is made in encrypted form via the public internet. The setup of a VPN is not completely trivial, which leads to the abandonment of security concerns at times and the data will be imprudently transmitted unencrypted via the internet. What dangers are possible, especially in industrial plants can be found in this article at heise.de.
Mesh Networking
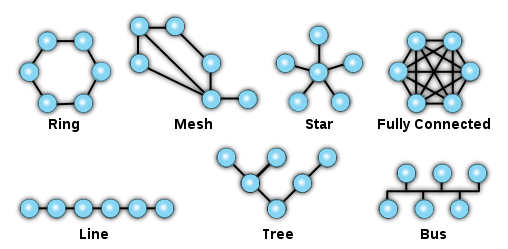
In a meshed network every node is connected one or more other nodes. The information is passed from one node to next until it reaches its destination. If every participant is connected to every other participant we talk about a fully meshed network. Meshed networks are usually self-healing and therefore very reliable. If a node or a connection is blocked or or fails the network around it can rebuild. Data will be redirected and the network remains operational. It is also easy to add new accounts or delete existing accounts without interrupting the transport of data.